DNMLinks Guide: How to Install and Secure Tor Browser
Learn how to download, install, and secure Tor Browser on Windows, macOS, Linux, Android, and iOS for anonymous browsing.
Introduction
Tor Browser is a powerful tool for enhancing your online privacy and anonymity. It routes your internet traffic through the Tor network, making it difficult to trace your activity back to you. This guide provides detailed instructions for installing and configuring Tor Browser on various platforms, along with essential security tips and information about JavaScript risks.
Step-by-Step Installation Guide
Step 1: Download Tor Browser
Always download Tor Browser from the official Tor Project website to ensure you get a legitimate and secure version.
Tor Project Download Page
Step 2: Installation by Platform
Step 3: Connect to the Tor Network
After installation, launch Tor Browser. You'll be presented with a connection screen. For most users, clicking the large "Connect" button is sufficient.
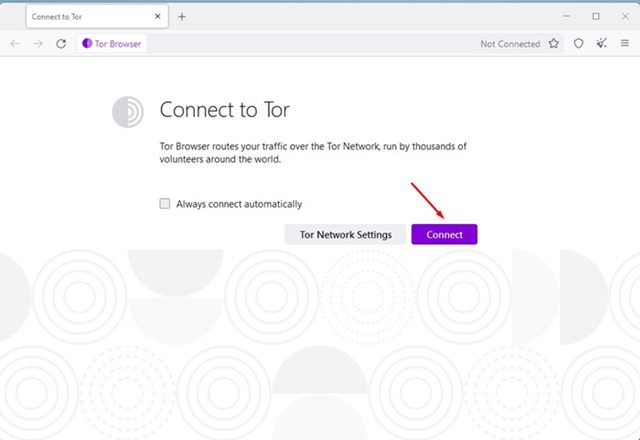
Tor Browser Connection Screen
Advanced Configuration (Optional)
If you need to configure a proxy, bridge, or other network settings, click the "Configure Connection" button (or the Tor onion icon, then "Connection settings") before connecting. This is usually only necessary if you are in a location with heavy internet censorship or if your network requires a proxy.
- **Bridges:** Bridges are unlisted Tor relays that help you circumvent censorship. Obtain bridge addresses from the Tor Project website or by emailing [email protected] (using a Gmail or Riseup account).
- **Proxy Settings:** If you need to use a proxy to access the internet, enter the proxy details in the connection settings.
Enhancing Tor Browser Security
While Tor Browser provides strong anonymity by default, you can take additional steps to further enhance your security and privacy:
- **Security Level:** Tor Browser has three security levels: Standard, Safer, and Safest. Access these settings by clicking the shield icon next to the address bar. 'Safer' disables JavaScript on non-HTTPS sites, and 'Safest' disables JavaScript on all sites. Higher security levels can break some website functionality.
- **Keep Tor Browser Updated:** Always use the latest version of Tor Browser to benefit from security patches and bug fixes. Tor Browser will usually prompt you when an update is available.
- **Don't Install Browser Extensions:** Avoid installing additional browser extensions, as they can potentially compromise your anonymity or introduce security vulnerabilities.
- **Use HTTPS Everywhere:** While Tor Browser encrypts your traffic within the Tor network, it's still important to use HTTPS websites whenever possible to ensure end-to-end encryption. Consider using the HTTPS Everywhere extension (often pre-installed).
- **Be Mindful of Your Online Activity:** Tor Browser protects your IP address and makes it difficult to track you, but it doesn't make you completely immune to all threats. Avoid downloading files from untrusted sources, clicking on suspicious links, or sharing personal information.
- **Don't Torrent over Tor:** Torrenting over Tor is strongly discouraged. It slows down the network for everyone and can potentially expose your real IP address.
- **Use a Reputable VPN (Optional):** For an additional layer of security, you can use a VPN in conjunction with Tor Browser. This can help protect you if there's a vulnerability in Tor itself and can make it more difficult to correlate your activity. Choose a VPN provider that respects privacy and doesn't keep logs.
- **New Identity:** Use the 'New Identity' feature (the broom icon) to get a fresh Tor circuit and clear all cookies and browsing history.
Understanding JavaScript Risks
JavaScript is a programming language used to make websites interactive. However, it can also be used to track you and potentially deanonymize you. Tor Browser's security levels help mitigate these risks.
- **Fingerprinting:** Websites can use JavaScript to collect information about your browser and system configuration (e.g., screen size, fonts, installed plugins). This information can be used to create a unique 'fingerprint' that can identify you even if you're using Tor.
- **Exploits:** Vulnerabilities in JavaScript engines can be exploited to run malicious code on your computer, potentially compromising your anonymity or security.
- **Cross-Site Scripting (XSS):** XSS attacks involve injecting malicious JavaScript into a legitimate website. This can allow attackers to steal cookies, hijack sessions, or redirect you to phishing sites.
Mitigation Strategies
- **Use Tor Browser's 'Safer' or 'Safest' Security Levels:** This is the most effective way to reduce JavaScript risks.
- **Disable JavaScript Selectively:** If you need JavaScript for a specific website, you can temporarily enable it using the NoScript extension (pre-installed in Tor Browser). However, be very careful about which sites you trust with JavaScript.
- **Keep Your Browser Updated:** Regular updates patch security vulnerabilities, including those related to JavaScript.
Additional Resources
Conclusion
By following these steps, you can successfully install and configure Tor Browser for secure and anonymous browsing. Remember to prioritize security and be mindful of your online activity to protect your privacy effectively. Regularly review the Tor Project's documentation and updates for the latest security recommendations.
Table of Contents
Related Articles
DNMLinks Guide: How to Buy Bitcoin & Withdraw to Electrum Wallet
Learn how to buy Bitcoin in different regions of the world, and securely withdraw Bitcoin to your Electrum wallet.
Read ArticleDNMLinks Guide: How to Install Electrum Bitcoin Wallet
Learn how to install Electrum, a secure and lightweight Bitcoin wallet, on Windows, macOS, and Linux.
Read ArticleDNMLinks Guide: How to Install Feather Wallet (Monero)
Learn how to install Feather Wallet, a privacy-focused Monero (XMR) wallet, on Windows, macOS, and Linux.
Read ArticleSecurity Tips
Essential security practices to stay safe when browsing darknet markets.
View Tips